# Custom authentication process (Pipeline)
# Introduction
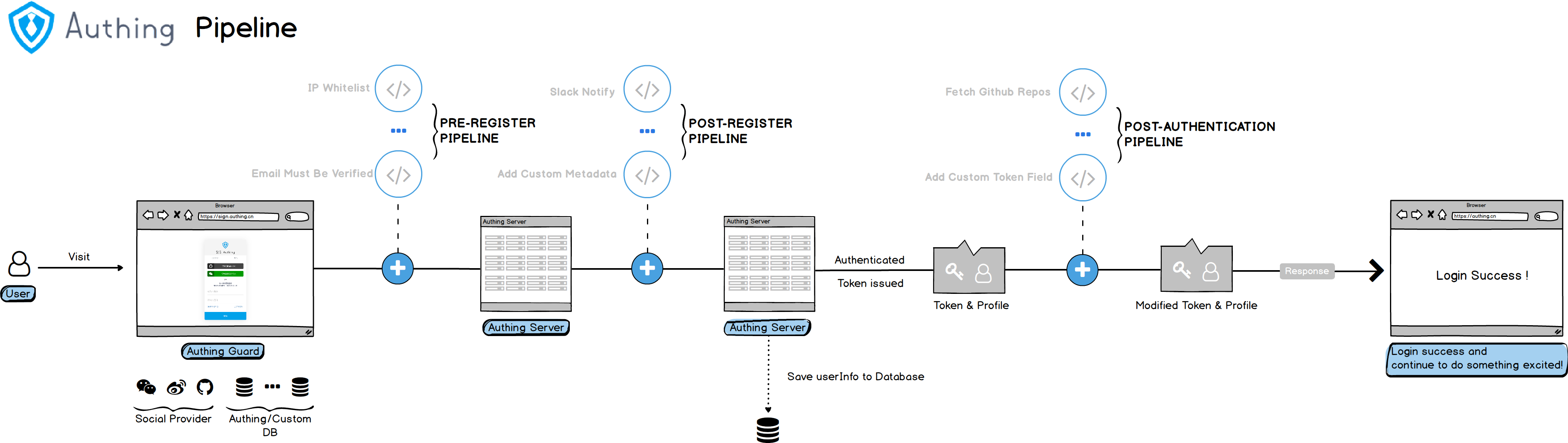
Authing Pipeline is a set of user-defined JavaScript code running in the cloud ☁️, which allows developers to extend and customize Authing capabilities.
Authing Pipeline functions are all user-definable, and we also provide rich function templates (opens new window) to help developers get started quickly.
At the same time, Pipeline is a set of functions. The difference from ordinary Hooks is that the function data in the entire pipeline can be transferred to each other to achieve the same effect as an industrial pipeline. This design pattern can make developers' custom functions more modular and easy to manage.
The backend of Authing Pipeline uses a serverless architecture, and all user-defined codes are run in the cloud to ensure isolation between different tenants, and at the same time, it can be elastically scalable, which not only ensures security, but also improves operating efficiency.
# Application scenario
With the help of Authing Pipeline, developers can achieve the following functions:
- Whitelist mechanism: such as the whitelist of registered mailbox suffixes, the whitelist of registered IPs, etc.
- Event notification: such as sending group notification after user registration, notification of user login IP exception, etc.
- Permission control: such as adding users to a user group based on their mailbox after logging in.
- Extended user field: add custom metadata to the requesting user as usual.
- Custom token: such as adding custom fields to the token.
- ... and more, the imagination is endless.
Next, let us create your first Pipeline function together!
Create your first Pipeline function