# Connect Azure Active Directory OIDC IdP
This article describes the use of Authing to connect to Azure Active Directory as an external identity source for authentication through the OIDC protocol. Introduced the opening of Azure Active Directory service in the Azure international zone, registration of the application, completing the OIDC identity source configuration steps, and configuring the Azure Active Directory connection in the Authing console, and using the created connection for authentication in Azure Active Directory.
# Create Azure Active Directory OIDC IdP
Log in to Azure (opens new window), search for Active Directory in the search box, and select "Azure Active Directory", as shown below:

Click "App Registration" on the left menu, and click "New Registration".

Fill in an application name and redirect URI: https://core.authing.cn/connections/oidc/callback, and finally click "register".

Find your application, go to the application overview page, and record the application ID.

On the left menu, click "Certificate and Password", and then click "New Client Password".

You can fill in a description for the key and click "Add".

Record the application key you just added.

Go back to the application overview page, click the "End Node" Tab, find the "OpenID Connect Metadata Document", and open the link in the browser.

Record the issuer content, as shown in the figure:

At this point, you have created an OIDC IdP in Azure, and recorded application ID, application key, issuer information, which will be filled in Authing.
# Create OIDC connection
In Authing Console> Connect Identity Source> Enterprise Identity Source, find Connect OIDC Identity Source, click "Create", and fill in issuer and application ID, as shown in the figure Shown:

Then find the OIDC connection you just created and click the edit button.

Find the mode, select "Back Channel", fill in the application key, and finally click "Save".

# Test connection
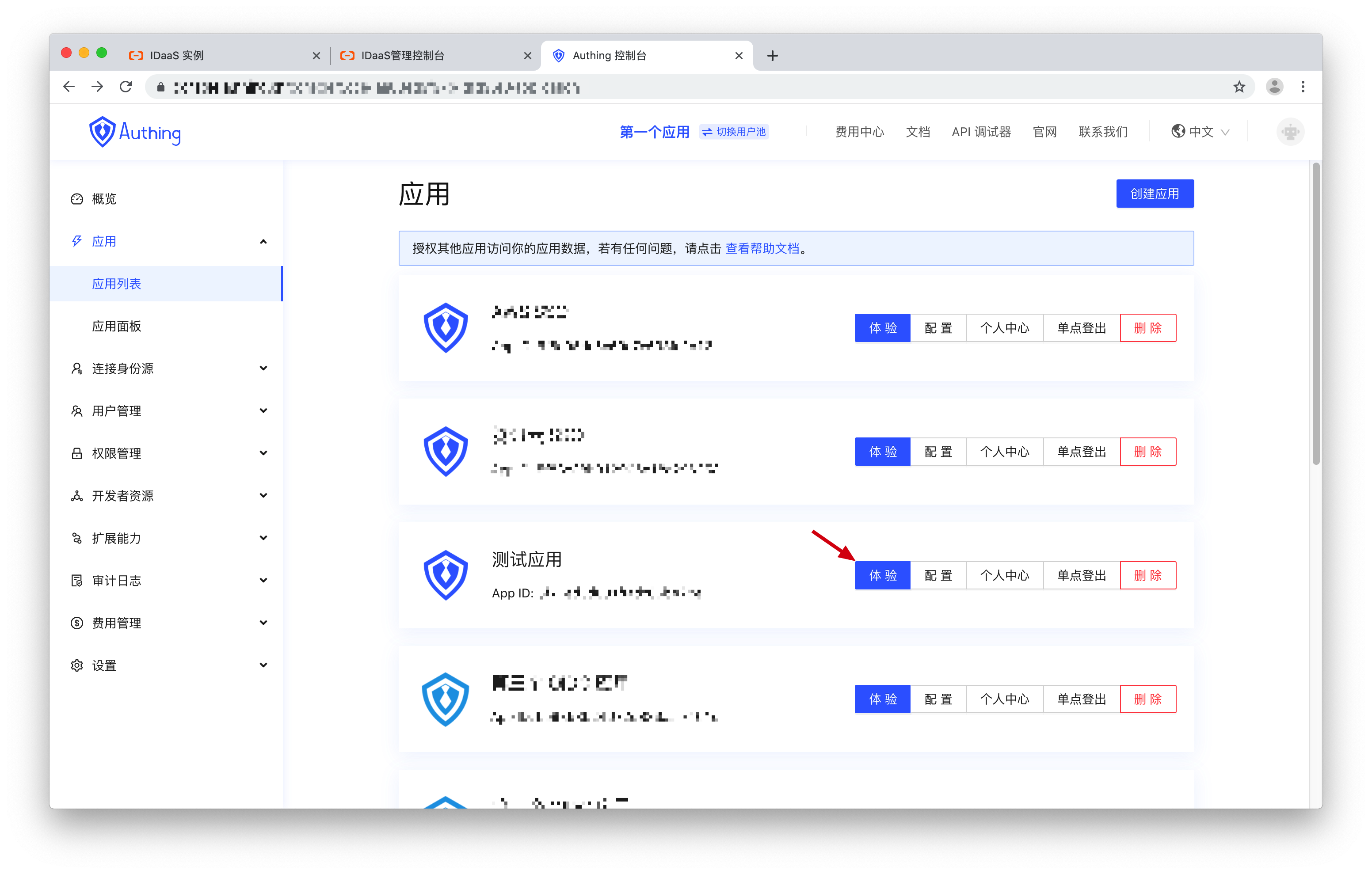
Go to Control Panel> Apps> App List, choose an app at will, and click "Experience".
On the login page, click "Log in with Azure SSO".

In the login box that pops up, complete the authentication in Azure Active Directory OIDC IdP.

Click "Accept" on the confirmation page.

login successful.

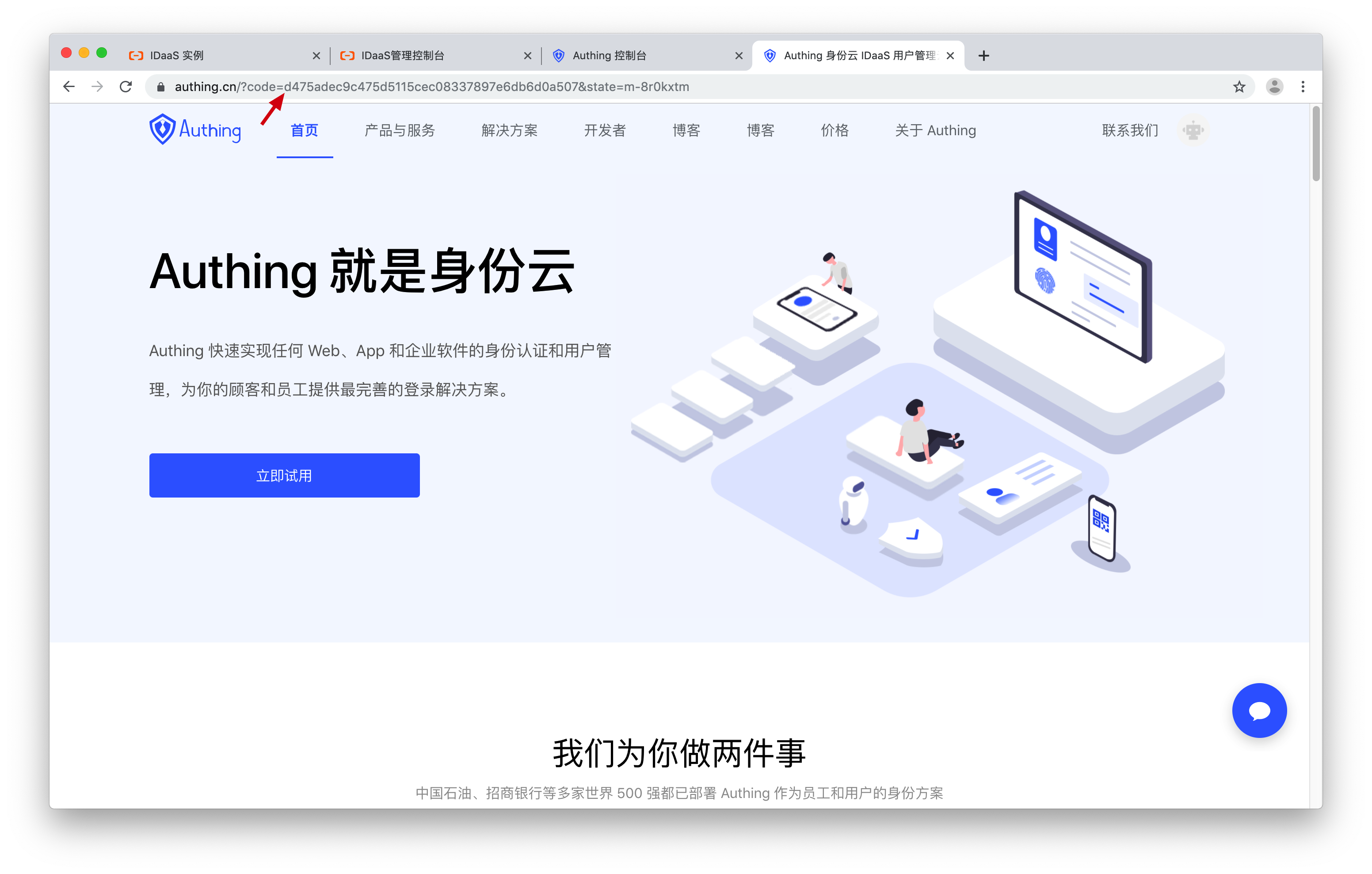
After successful login, jump to the callback address and carry the code authorization code.
# Next you may need
Use authorization code in exchange for user information:
Use OIDC authorization